Every day over 5 mln people use signNow for various business and personal purposes.
By many of these users, signNow is seen as just a “digital pen” and also a cloud storage: you e-sign, send and store documents – as simple as that.
But there are also more detail-oriented users who ask themselves the following “what-if” questions:
What if the signer changes his/her mind after signing a document? What if somebody, somehow, uses the signing link instead of the intended signer? What if the recipient never gets my document?
Check all document changes with Audit Trail
No worries, we got you covered! signNow has Audit Trail and Document History to answer all of these (and many other) questions that you might have.
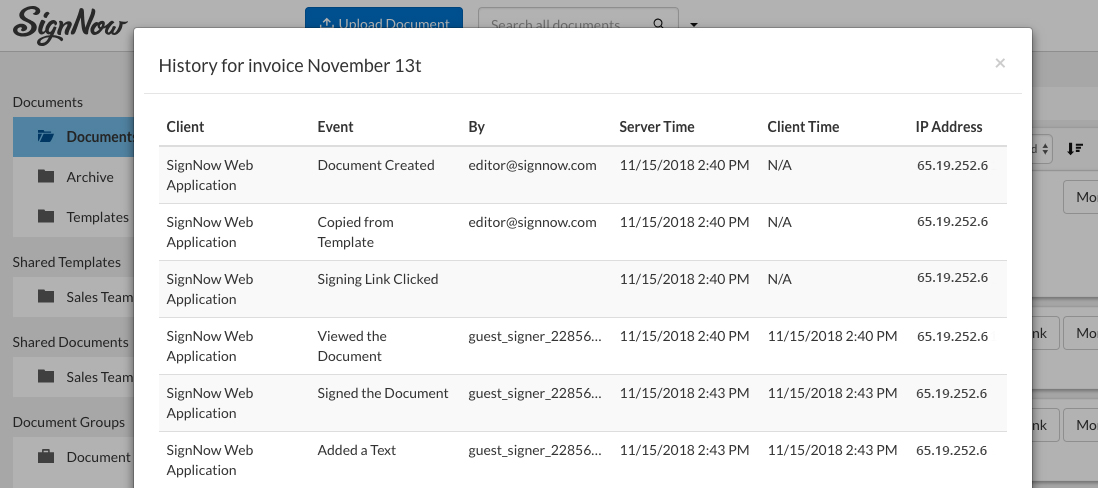
To access Document History, click on the More button next to the document that you want to track. Then, select History in the dropdown menu. You will get a pop-up table with the following information:
- Client – In this case, it’s the mode of action: on a browser page, via a mobile device, within an integration with another software/app;
- Event – what action specifically has been done to the document;
- By – email credentials of the user
- And then also – the Server Time, the Client Time and the IP address of the user.
There are three broad categories of cases when audit trail can work really well in your favour:
First: when proving personal attribution
Or in other words, when answering the question “Who REALLY signed this?”
As the court cases HERE and HERE clearly show, audit trail serves as fully court-admissible evidence that proves who had access to a particular document, who made changes in it, who signed it and exactly when/where all of this took place.
Excuses like “We never got an email from you” or “You probably sent the document to the wrong guy who signed it by mistake” will never work here.
The key factor here as to why our audit trail data is treated as court-admissible is because it is fully compliant with all UETA regulations regarding attribution.
Second: When proving that a certain action was applied to your document (or when no action at all when one was needed)
This category involves plenty of unfortunate cases: a doctor’s negligence or wrong diagnosis indicated in personal medical records and police or prison brutality which somebody tried to cover up by changing information in official records are just two of many examples. An expansive archive of similarly grievous cases can be found HERE and HERE.
Unfortunately, in the majority of such cases, it is already too late to try to fix everything with an audit trail – due to the irreversible nature of the damages caused. However, you can at least make sure that justice is restored.
Also note that having the option of audit trail for all electronic records and eSignatures is one of the core requirements for HIPAA compliance. This means that any hospital/pharmacy/drug manufacturer claiming to be HIPAA compliant is supposed to provide their audit logs when asked to do so by the court.
Third: when you need better monitoring over internal business processes
Audit trail can actually be used not only externally, but also internally – inside your own organization/team.
This is especially helpful if you are using Shared Documents & Templates in SignNow.
The details provided in the audit log may supply you with some very useful info. You can check which of your team members opened certain files, and when exactly they did so. You can even track the IP address to give you an idea as to where a file was opened (for example, we all know perfectly well that some internal files should never be opened in a Starbucks two blocks from your office, right?).
signNow’s Audit Trail makes sure you always come prepared in case anything goes wrong. Now you can always prove the who, what, when, why, and how of the storyline for any document.